API Keys
API keys control access to your Sprigr Teams workspace through MCP. Each key is linked to the user who creates it and inherits that user’s data visibility, giving you secure, role-based access from any MCP client.
Creating an API key
Section titled “Creating an API key”-
Navigate to the MCP page
Sign in to team.sprigr.com and click MCP in the sidebar.
-
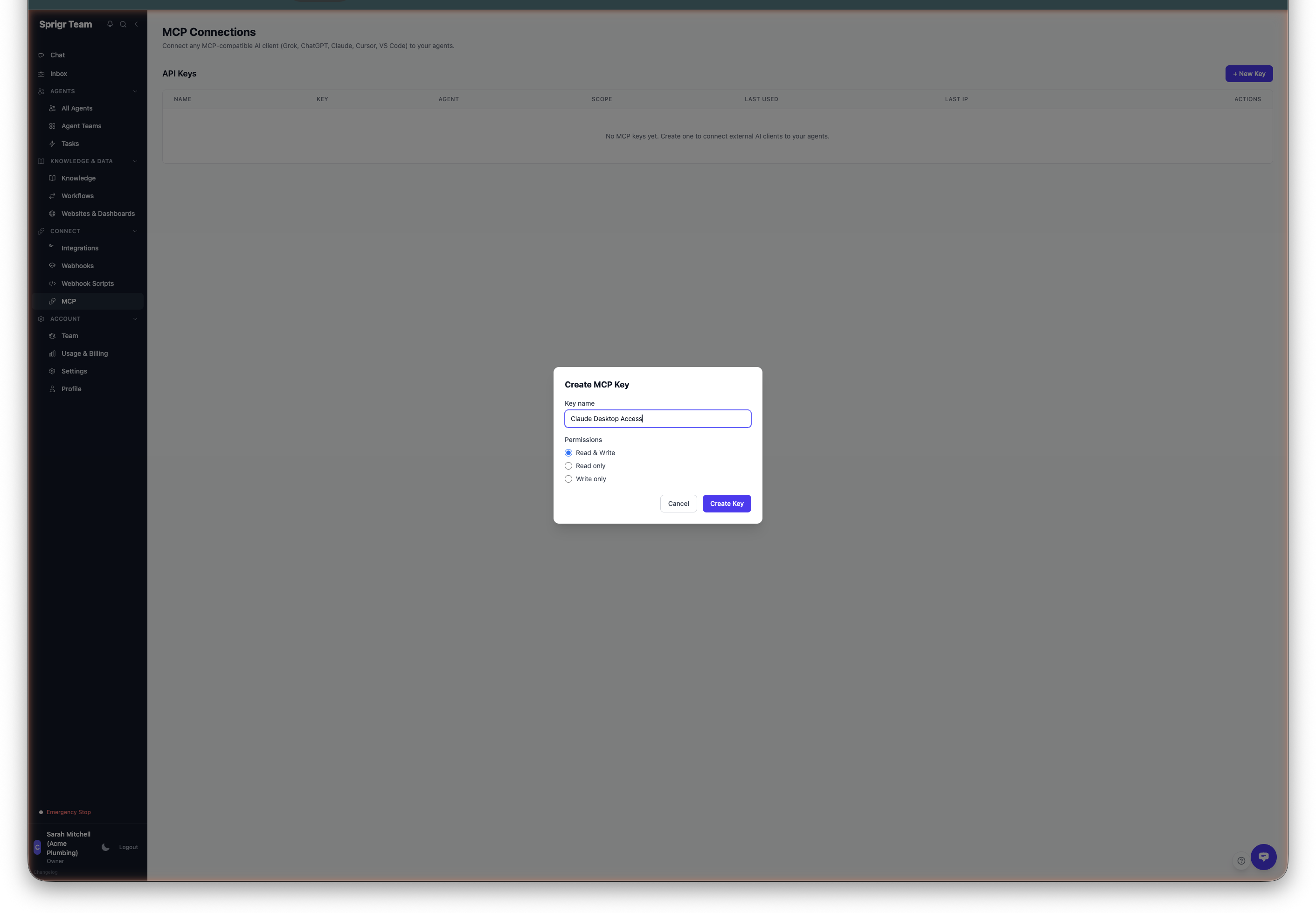
Click ”+ New Key”
Click the + New Key button to open the key creation form.
-
Enter a name
Give the key a descriptive name that identifies its purpose, such as “Claude Code - Chris” or “Cursor IDE - Dev Team”. This helps you manage multiple keys later.
-
Select a scope
Choose the level of access this key should have:
Scope Tools available Description Read only 21 read tools Can list agents, search knowledge, view workflows, check usage. Cannot send messages or make changes. Write only 20 write tools Can send messages, create agents, manage workflows. Cannot read lists or search. Read & Write All 41 tools Full access to both read and write operations. This is the most common choice. -
Optionally scope to a specific agent
By default, a key can access all agents in your workspace (subject to the user’s role — see permissions below). If you want to restrict the key to a single agent, select that agent from the dropdown. The key will only be able to interact with that specific agent.
-
Copy the key
After clicking Create, the API key is displayed once. Copy it immediately and store it securely — you will not be able to see the full key again. If you lose it, you will need to create a new one.
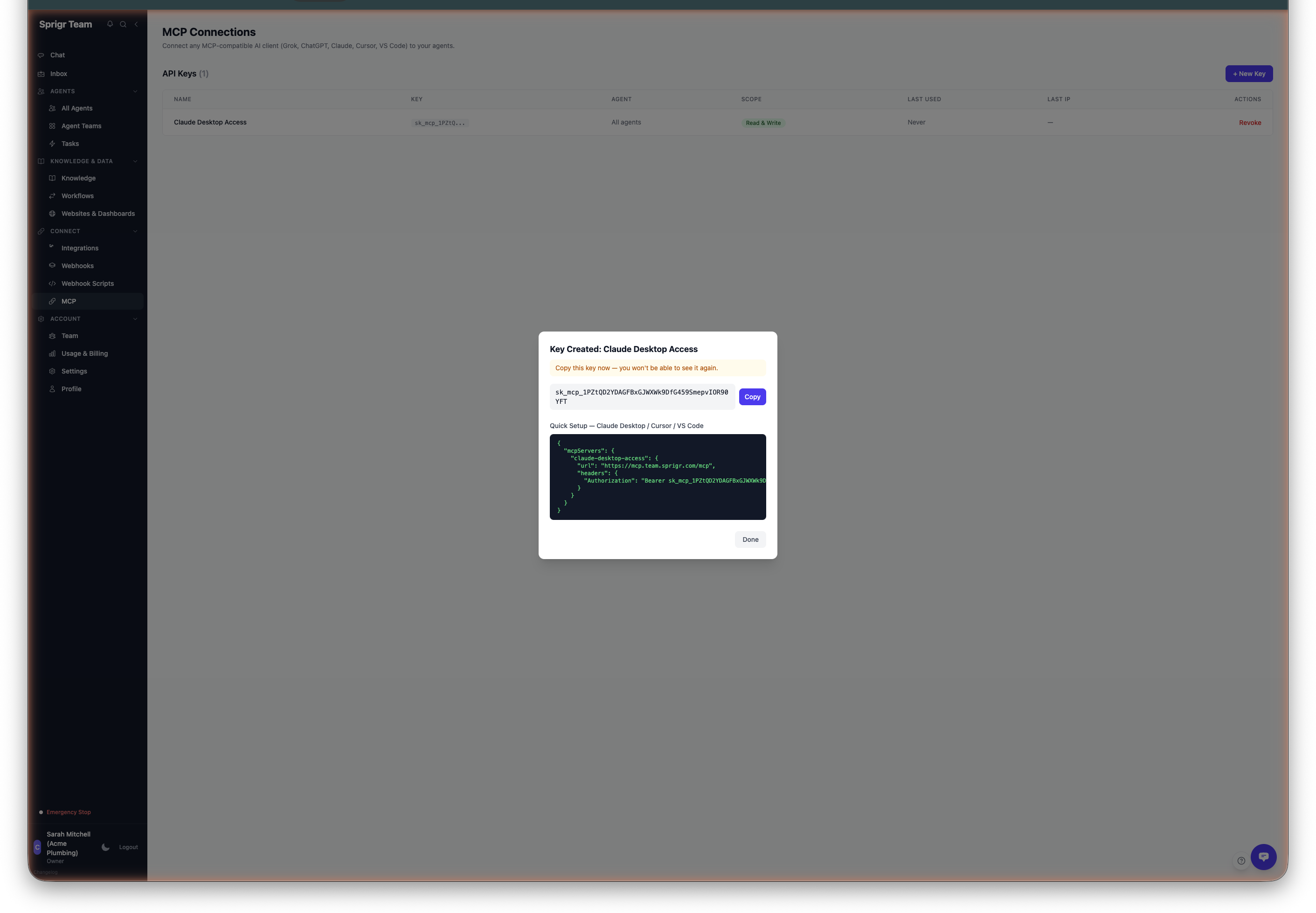
Your new key will appear in the API Keys table with its name, prefix, scope, and last-used timestamp.
User-level permissions
Section titled “User-level permissions”Every MCP key is permanently linked to the user who created it. The key inherits that user’s role and data visibility:
- Owner/Admin users — Keys created by admins or owners can see all agents, all conversations, all threads, and all company data. They have the same unrestricted view as the portal dashboard.
- Member users — Keys created by members can only see agents they are assigned to and their own conversations. This is the same restriction they experience in the portal.
This is enforced automatically. You do not need to configure it — the platform looks up the creating user’s role on every request and applies the appropriate data filtering.
All 41 tools remain available regardless of user role. The role only affects what data comes back. A member calling list_agents sees their assigned agents. An admin calling list_agents sees all agents.
Connecting to MCP clients
Section titled “Connecting to MCP clients”The MCP server URL for your workspace is:
https://mcp.team.sprigr.com/mcpClaude Code
Section titled “Claude Code”Claude Code supports remote HTTP MCP servers natively. Add it with a single command:
claude mcp add --transport http "sprigr-hq" https://mcp.team.sprigr.com/mcp --header "Authorization: Bearer sk_mcp_YOUR_KEY_HERE"Or add it directly to your ~/.claude/settings.json:
{ "mcpServers": { "sprigr-hq": { "url": "https://mcp.team.sprigr.com/mcp", "headers": { "Authorization": "Bearer sk_mcp_YOUR_KEY_HERE" } } }}The server will be available in your next Claude Code session. All 41 tools appear automatically.
Claude Desktop
Section titled “Claude Desktop”Claude Desktop requires a stdio-to-HTTP bridge for remote MCP servers. Add the following to your claude_desktop_config.json:
macOS: ~/Library/Application Support/Claude/claude_desktop_config.json
Windows: %APPDATA%\Claude\claude_desktop_config.json
{ "mcpServers": { "sprigr-hq": { "command": "npx", "args": [ "-y", "mcp-remote", "https://mcp.team.sprigr.com/mcp", "--header", "Authorization: Bearer sk_mcp_YOUR_KEY_HERE" ] } }}Restart Claude Desktop after saving. The server and all 41 tools will appear in your next conversation.
Cursor, VS Code, and other clients
Section titled “Cursor, VS Code, and other clients”Add the following to your MCP client configuration. The transport type is Streamable HTTP.
{ "mcpServers": { "sprigr-hq": { "url": "https://mcp.team.sprigr.com/mcp", "headers": { "Authorization": "Bearer sk_mcp_YOUR_KEY_HERE" } } }}Managing API keys
Section titled “Managing API keys”The MCP page lists all active API keys for your organisation. For each key, you can see:
- Name — The descriptive name you assigned
- Scope — Read only, Write only, or Read & Write
- Agent scope — All agents or a specific agent
- Created by — The user who created the key (whose permissions it inherits)
- Created date — When the key was created
- Last used — When the key was last used to make a request
- IP address — The IP address of the most recent request
Revoking a key
Section titled “Revoking a key”To revoke a key, click the delete icon next to it on the MCP page. Revoking a key is immediate — any client using that key will lose access as soon as the key is deleted. There is no way to reactivate a revoked key; you must create a new one.
IP tracking
Section titled “IP tracking”Sprigr Teams logs the IP address of every request made with an API key. When a new IP address is detected for a key, an alert is triggered. This information is displayed on the MCP page and can help you:
- Verify that keys are being used from expected locations
- Detect unexpected access from unfamiliar IP addresses
- Audit key usage across your organisation
Best practices
Section titled “Best practices”- One key per person or application — Create separate keys for each team member or tool that needs MCP access. This makes it easy to revoke access for a specific person or tool without affecting others.
- Use Read & Write for most cases — Most users need both read and write access. Reserve read-only keys for monitoring dashboards or automated reporting.
- Scope keys when possible — If a key is only used to interact with one agent, scope it to that agent.
- Rotate keys regularly — Periodically create new keys and revoke old ones, especially for keys used in shared environments.
- Remember user binding — Each key is permanently tied to the user who created it. If a team member leaves, revoke their keys.
Next steps
Section titled “Next steps”- MCP Overview — Learn how MCP works with Sprigr Teams, including the full list of 41 tools.
- Creating Agents — Create agents that MCP clients can interact with.
- Knowledge Bases — Set up knowledge bases that MCP clients can search.